AI-Powered Quantum-Resistant Authentication and Key- Management System
Keywords:
- Neural cryptography,
- AI-driven security systems,
- Quantum-resistant authentication,
- Self-monitoring network architecture,
- Amplitude encoding
Abstract
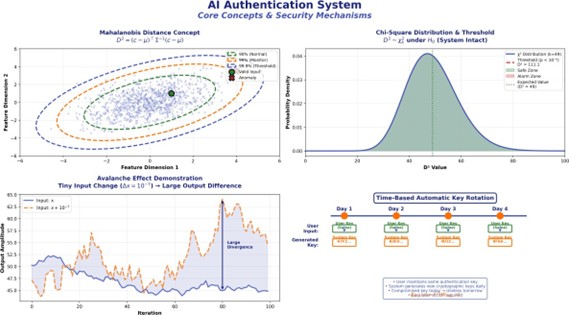
The accelerating convergence of AI, high-performance computing and cryptography is rapidly transforming both security paradigms and attack surfaces. Current authentication and key management systems are increasingly threatened not only by the advent of quantum computing, but also by the exponential growth of HPC clusters and AI-driven attack techniques. Brute-force and novel side-channel attacks are becoming increasingly feasible, while most cryptographic solutions lack autonomous, real-time self-monitoring and effective resistance to advanced intrusion attempts. We present a dual-neural architecture for authentication and key management that integrates a primary authentication network and a watchdog integrity layer. This cryptographic prototype system employs classical AES-256 encryption for message confidentiality and leverages neural network–based amplitude encoding for robust, non-invertible key protection. Real-time integrity monitoring is achieved by a secondary (watchdog) network, enabling immediate detection of system tampering and attack attempts.
Empirical evaluation of the cryptographic neural network demonstrates a persistent invariant, with inter-layer Pearson correlation coefficients reaching 0.999x ± y across extensive test scenarios. These invariants underpin the system’s resilience, allowing for tamper detection, avalanche sensitivity and secure, one-way mapping of cryptographic keys to amplitude states. The mathematical principles and topological invariants applied here were originally identified in a separate research neural network with over one million data points; in this work, however, all reported results and benchmarks are derived solely from the cryptographic prototype.
This architecture represents a step toward dynamic, self-monitoring security systems capable of resisting both conventional and emerging threats, including those posed by quantum computing and AI-driven attack vectors. This work extends foundational results from self-regulating neural systems and non-local information spaces, as introduced in our previous studies and integrates established cryptographic, quantum-resistant and AI-driven security concepts. Here, the numbers refer to the full references listed in the References section at the end of this preprint. Together, these sources provide the scientific basis for the proposed architecture and situate it within the state-of-the-art at the intersection of neural computation and secure information management.
Downloads
References
Trauth S (2025) Emergent quantum entanglement in self-regulating neural networks. Zenodo. https://zenodo.org/records/14952782
Trauth S (2025) The 255-bit non-local information space in a neural network: Emergent geometry and coupled curvature-tunneling dynamics in deterministic systems. Zenodo. https://zenodo.org/records/17406341
Boneh D, Shoup V (2020) A graduate course in applied cryptography. https://r.jordan.im/download/technology/BonehShoup_0_5.pdf
L Chen, F Cheng (2019) Quantum-resistant cryptography: A survey. IEEE.
Rivest RL, Shamir A, Adleman L (1978) A method for obtaining digital signatures and public-key cryptosystems. Comm ACM 21: 120-126. https://dl.acm.org/doi/abs/10.1145/359340.359342
He K, Zhang X, Ren S, Sun J (2015) Delving deep into rectifiers: Surpassing human-level performance on imagenet classification. IEEE Int Conf Comput Vis 1026-1034. https://ieeexplore.ieee.org/document/7410480
Yuan Y, Lu X, Wang Y (2022) AI-driven security: Threat intelligence and automated defense. IEEE Trans Industr Inform. 18: 1234-1245.